Master the Vulnerability Management Process for SME Compliance
- Gary Sinnott

- 3d
- 7 min read
Managing Cyber Essentials compliance can feel like a moving target for IT leaders at British legal and financial firms. As regulations change and risks become more sophisticated, the need for a robust vulnerability management policy grows stronger. The UK Government Cyber Security unit advises constantly refining your security strategies to meet national standards. This guide offers practical steps and expert vCISO insights to help you build operational resilience and stay ahead of threats.
Table of Contents
Summary of Key Insights
Main Insight | Detailed Explanation |
1. Create a Vulnerability Policy | Establish a strong policy to guide vulnerability management, aligning with national standards and addressing critical components like risk assessment and remediation. |
2. Deploy Detection Tools | Utilize advanced tools for asset and threat discovery, ensuring real-time monitoring and comprehensive visibility of your technology ecosystem. |
3. Conduct Regular Assessments | Implement systematic vulnerability assessments that combine automated scans with expert analysis for a thorough understanding of security risks. |
4. Prioritise Risks Effectively | Use severity scoring and risk impact assessments to prioritise remediation efforts based on potential business disruption and vulnerability criticality. |
5. Validate Security Measures | Continuously validate implemented security measures through independent testing and audits to ensure effective risk reduction and compliance with regulations. |
Step 1: Establish a Vulnerability Management Policy
Establishing a robust vulnerability management policy is crucial for protecting your organisation’s digital infrastructure and maintaining compliance. This foundational document will guide your approach to identifying, assessing, and mitigating security risks across your entire technology ecosystem.
Your vulnerability management policy should comprehensively address several critical components to ensure a structured and proactive approach. The UK Government Cyber Security unit recommends developing comprehensive vulnerability strategies that align with national cybersecurity standards. Key elements include:
Risk assessment framework defining vulnerability severity levels
Clear responsibilities for security team members
Processes for continuous vulnerability scanning
Procedures for remediation and incident reporting
Compliance requirements for all technology assets
When drafting the policy, consider adopting a secure by design principle that integrates security considerations into every stage of your technological infrastructure. This means creating a living document that evolves with your organisation’s changing technological landscape and emerging threat environments.
Implementing this policy requires cross-departmental collaboration. Your IT, security, and management teams must collectively understand and commit to the vulnerability management approach. Regular training and communication will help embed these practices into your organisational culture.
Here is an overview of common vulnerability management roles and their responsibilities:
Role | Primary Responsibility | Collaboration Focus |
IT Team | Implements technical controls and monitors assets | Coordinates with security |
Security Team | Conducts vulnerability assessments and analysis | Engages with management |
Management | Approves policies and allocates resources | Oversees compliance efforts |
Asset Owners | Maintains asset integrity and reporting | Supports remediation actions |
Professional Advice: Conduct an annual review of your vulnerability management policy to ensure it remains current with evolving cybersecurity threats and technological changes.
Step 2: Deploy Tools for Asset and Threat Discovery
Deploying sophisticated tools for asset and threat discovery is a critical step in establishing a comprehensive vulnerability management strategy. Your goal is to create a complete inventory of your technological ecosystem and identify potential security weaknesses before they can be exploited.
The Information Commissioner’s Office recommends comprehensive asset discovery processes that go beyond simple hardware tracking. Key tools and techniques for effective asset discovery include:
Network scanning tools to map all connected devices
Software inventory management platforms
Automated vulnerability assessment systems
Network traffic analysis solutions
Endpoint detection and response (EDR) technologies
When selecting discovery tools, prioritise solutions that provide real-time monitoring and comprehensive visibility across your entire technology infrastructure. Integration capabilities are crucial, allowing different security tools to communicate and provide a holistic view of your organisation’s digital landscape.
Effective asset discovery is not a one-time event, but a continuous process of monitoring and updating your technological inventory.
Implement a systematic approach to categorising discovered assets based on their criticality, data sensitivity, and potential security risks. This enables your security team to prioritise remediation efforts and allocate resources more effectively.
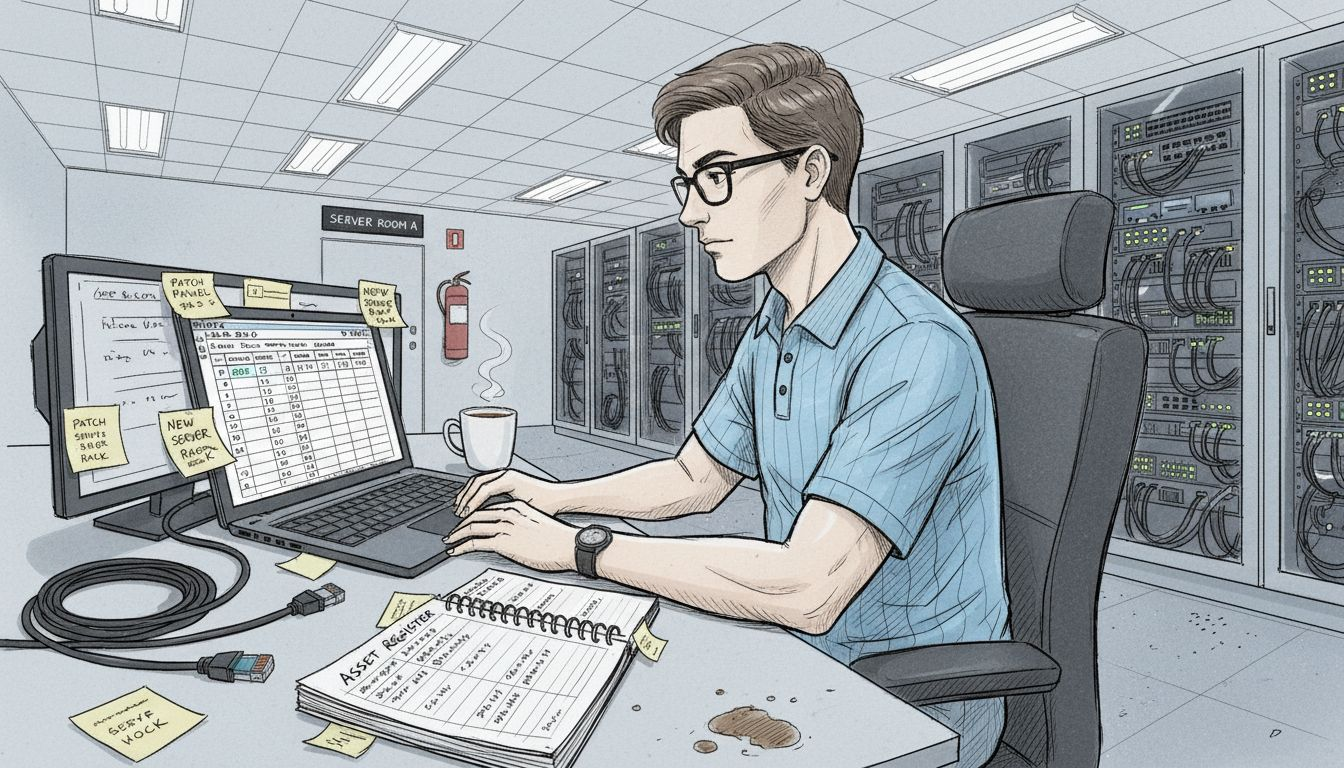
Professional Advice: Conduct quarterly comprehensive scans to ensure your asset inventory remains current and accurately reflects your organisation’s technological environment.
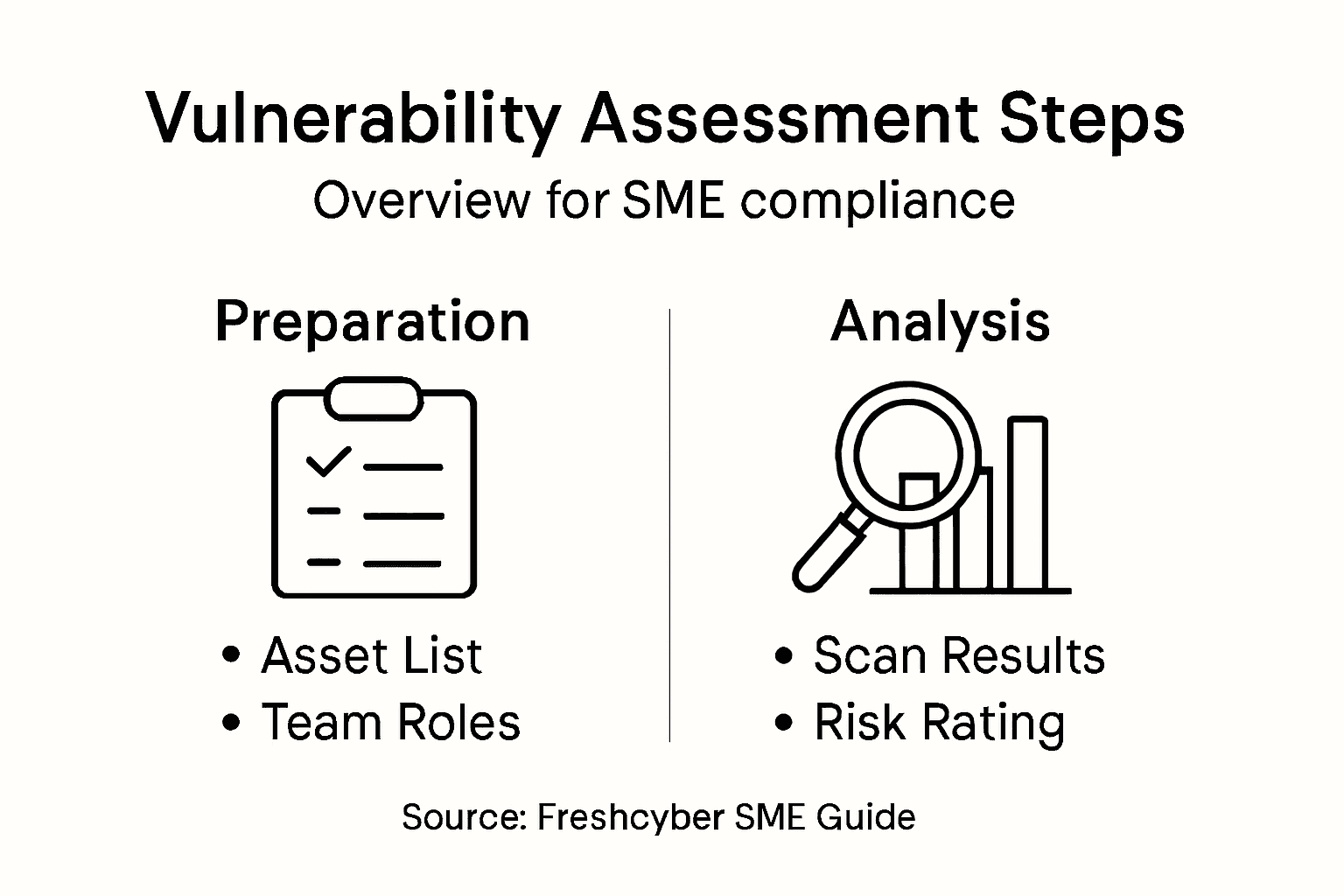
Step 3: Conduct Systematic Vulnerability Assessments
Conducting systematic vulnerability assessments is a critical process for identifying and mitigating potential security risks within your organisation’s technological infrastructure. Your objective is to create a comprehensive and methodical approach to understanding and addressing potential vulnerabilities before they can be exploited.
The National Protective Security Authority recommends comprehensive role-based risk assessments that examine technical, physical, and human factors. Key components of an effective vulnerability assessment include:
Detailed network infrastructure mapping
Comprehensive software and hardware inventory
Threat modelling and risk prioritisation
Penetration testing and simulated attack scenarios
Detailed reporting and documentation
Vulnerability assessments are not a one-time event, but a continuous process of monitoring, identifying, and addressing potential security weaknesses.
Each assessment should follow a structured methodology that combines automated scanning tools with expert human analysis. Technical depth and contextual understanding are crucial in identifying nuanced vulnerabilities that might be missed by automated systems alone.
When conducting assessments, focus on creating a holistic view of your security landscape. This means looking beyond technical vulnerabilities to understand how organisational processes, human factors, and technological infrastructure interact to create potential security risks.
Professional Advice: Develop a standardised assessment template that can be consistently applied across different technological environments, ensuring comprehensive and comparable results.
Step 4: Prioritise and Remediate Identified Risks
Prioritising and remediating identified security risks is a critical process that transforms vulnerability assessments from theoretical exercises into tangible security improvements. Your goal is to systematically address vulnerabilities based on their potential impact and likelihood of exploitation.
The Information Commissioner’s Office emphasises comprehensive risk management procedures that go beyond simple identification. Key strategies for effective risk prioritisation include:
Severity scoring using standardised frameworks like CVSS
Risk impact assessment based on potential business disruption
Classification of vulnerabilities by criticality
Resource allocation for remediation efforts
Tracking and verification of resolved issues
Not all vulnerabilities are created equal. Prioritisation requires a strategic approach that balances technical risk with business context.
Establish a risk register that documents each identified vulnerability, its potential consequences, and recommended mitigation strategies. This living document should be regularly updated and reviewed to ensure your organisation maintains a proactive security posture.
Implement a structured remediation workflow that assigns clear ownership, sets realistic timelines, and provides mechanisms for tracking progress. Technical teams must collaborate with management to ensure that remediation efforts align with broader business objectives and resource constraints.
Professional Advice: Create a standardised remediation template that includes vulnerability details, risk score, assigned owner, proposed mitigation, and expected completion date.
Step 5: Validate Security Improvements and Compliance
Validating security improvements and compliance is the critical final phase of your vulnerability management process. Your objective is to systematically confirm that implemented security measures effectively reduce organisational risk and meet regulatory requirements.
The UK Government Cyber Unit emphasises comprehensive security validation processes that go beyond theoretical assessments. Key validation strategies include:
Continuous vulnerability scanning
Independent penetration testing
Compliance documentation review
External security audits
Performance metric tracking
Validation is not a destination, but an ongoing journey of continuous improvement and vigilance.
Technical validation requires a multifaceted approach that combines automated tools with expert human analysis. This means not just checking compliance boxes, but understanding the deeper security implications of your implemented controls.
Establish a robust reporting framework that provides transparent documentation of your security improvements. This should include detailed evidence of remediation efforts, current risk posture, and measurable improvements in your organisation’s security resilience.
This table summarises key security validation methods and their effectiveness:
Validation Method | Typical Frequency | Strengths | Limitations |
Continuous Scanning | Weekly or monthly | Rapid detection, wide coverage | May miss complex risks |
Penetration Testing | Annually or biannually | Reveals real-world exploitation | Costly and resource-intensive |
External Audit | Yearly | Unbiased review, regulatory trust | Limited technical depth |
Compliance Review | Quarterly | Confirms adherence to standards | Focuses on documentation |
Professional Advice: Conduct biannual comprehensive security assessments that provide a holistic view of your evolving cybersecurity landscape.
Strengthen Your SME’s Vulnerability Management with Freshcyber
Mastering the vulnerability management process is vital for SMEs aiming to achieve true compliance and digital resilience. If you struggle with managing ever-evolving security policies, continuous asset discovery, or prioritising remediation tasks, you are not alone. The challenges of creating a dynamic vulnerability management strategy and maintaining ongoing validation often overwhelm resource-constrained businesses seeking to meet regulatory requirements and protect sensitive data.
Freshcyber understands these pain points intimately. Our Vulnerability Management solutions are designed specifically to help SMEs turn complex compliance into strategic business value. With our unique Compliance Currency Engine and expert vCISO leadership, we provide comprehensive risk and policy management that keeps your organisation audit-ready and secure. Coupled with 24/7 MDR for proactive threat detection, we ensure your security improvements are validated continually—not just ticking boxes but building trust with your clients.

Take control of your vulnerability management journey today. Explore how Freshcyber’s tailored approach can transform your cybersecurity challenges into competitive advantages. Visit Freshcyber and discover the full range of SME Security and Compliance services designed to safeguard and grow your business.
Frequently Asked Questions
How do I establish a vulnerability management policy for my SME?
Establishing a vulnerability management policy involves defining risk levels, assigning responsibilities, and implementing continuous scanning processes. Draft a comprehensive document that evolves with your organisational needs and ensures all team members are engaged.
What tools should I use for asset and threat discovery?
Utilise network scanning tools, software inventory management platforms, and automated vulnerability assessment systems to create a complete inventory of your technological ecosystem. Prioritise tools that allow for real-time monitoring and provide comprehensive visibility of your assets.
How often should I conduct vulnerability assessments in my organisation?
Conduct vulnerability assessments systematically, ideally on a quarterly basis, to ensure you are consistently identifying potential risks. Establish a standardised template for assessments to maintain consistency and comparability across different environments.
What is the best way to prioritise and remediate identified vulnerabilities?
Prioritise vulnerabilities based on their severity and potential impact using established frameworks like CVSS. Create a risk register to document each vulnerability, assign ownership, and set realistic timelines for remediation to systematically address the most critical issues.
How can I validate that security improvements are effective?
Validate security improvements by performing independent penetration testing and continuous vulnerability scanning. Establish a reporting framework to document remediation efforts and track improvements in your organisation’s risk posture regularly.
Recommended
Comments