Master Vulnerability Management Process 2026 for SMEs
- Gary Sinnott

- Nov 28, 2025
- 7 min read

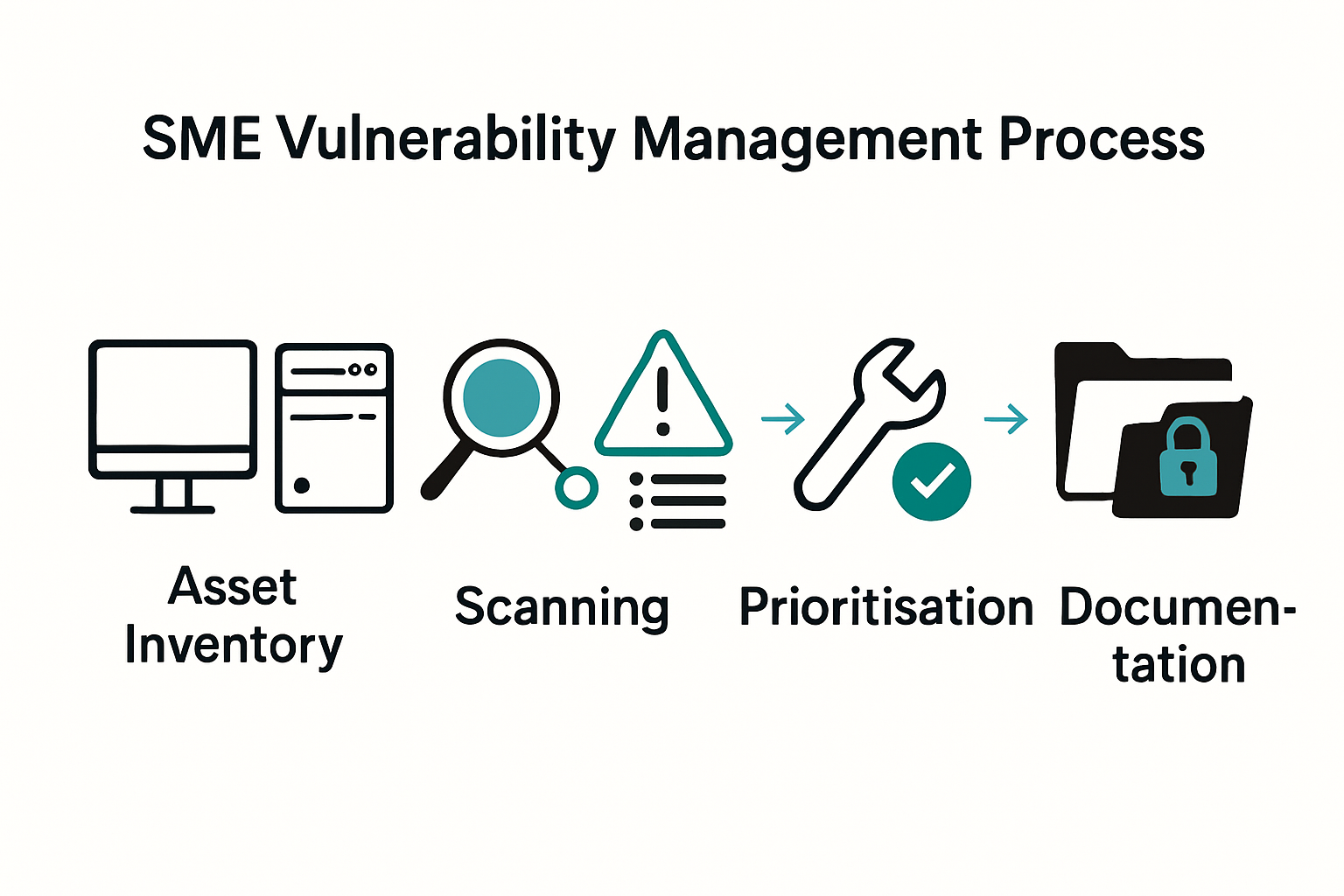
Most British organisations face a surprising truth - over 60 percent have incomplete visibility over their digital assets, leaving them exposed to security threats. Staying ahead of vulnerabilities matters more than ever as cyber risks increase and regulatory demands tighten. This guide shares practical steps any British leader can use to assess systems, deploy scanning tools, prioritise threats, remediate issues, and keep records that stand up to scrutiny.
Table of Contents
Quick Summary
Key Insight | Explanation |
1. Conduct a comprehensive asset inventory | Identify all networked devices and digital assets to manage vulnerability effectively. |
2. Establish regular scanning protocols | Implement monthly vulnerability scans and immediate assessments after significant system changes. |
3. Prioritise vulnerabilities based on impact | Use a scoring system to classify vulnerabilities, ensuring focus on the most critical threats first. |
4. Develop a structured remediation plan | Address identified vulnerabilities promptly and ensure successful implementation of fixes through verification. |
5. Maintain thorough documentation | Create records of vulnerability management activities to ensure accountability and compliance. |
Step 1: Assess current systems and define scope
Successfully managing vulnerability requires a strategic approach to understanding your organisation’s technological landscape. In this first critical stage, you will map out your current systems and establish a comprehensive scope for your vulnerability management process.
Begin by conducting a thorough inventory of all digital assets within your organisation. According to Security.gov.uk, Stage 1 focuses on capturing an overall view of your organisation’s mission and understanding the operating environment. This means identifying every networked device, server, application, cloud service, and digital endpoint that could potentially represent a security risk.
To define your scope effectively, create a detailed document that categorises systems by their criticality and potential impact. Security.gov.uk recommends capturing high-level details of critical systems and documenting them systematically. Prioritise systems that support essential services and have the most significant potential for business disruption if compromised.
Pro Tip: Don’t just list systems. Understand their interconnectedness and potential vulnerability pathways.
Your next step will involve conducting an initial risk assessment to prioritise which systems require immediate attention and deeper vulnerability scanning.
Step 2: Deploy scanning tools and schedule regular checks
Deploying effective vulnerability scanning tools and establishing a consistent checking schedule are crucial for maintaining robust cybersecurity across your organisation. In this stage, you will select appropriate scanning solutions and create a systematic approach to identifying potential security weaknesses.
According to NCSC, organisations should aim to perform vulnerability scans at least once per month or immediately following significant system changes. This means selecting automated scanning tools that can comprehensively assess your digital infrastructure, including web applications, network devices, and critical server environments. When choosing your scanning tools, prioritise solutions that offer continuous monitoring capabilities and can integrate seamlessly with your existing technology stack.
The scanning frequency will depend on your organisation’s complexity and risk profile. Security Guidance recommends weekly scans for internet-facing websites and digital services, with additional immediate scans after substantial configuration updates. Develop a standardised scanning schedule that covers all critical systems, ensuring you capture potential vulnerabilities before they can be exploited.
Pro Tip: Configure your scanning tools to generate clear, actionable reports that highlight critical vulnerabilities by severity and potential business impact.
With your scanning infrastructure in place, you are now prepared to move towards the next phase of comprehensive vulnerability management.

Step 3: Identify and prioritise vulnerabilities
Identifying and prioritising vulnerabilities is a critical process that transforms raw scanning data into actionable security insights. Your goal in this stage is to systematically evaluate potential security weaknesses and determine which require immediate attention.
According to Security.gov.uk, implementing an effective vulnerability management process involves establishing clear protocols to identify, assess, and prioritise potential security risks. Begin by categorising vulnerabilities based on their potential impact, considering factors such as exploitability, potential damage, and ease of remediation. Government Guidance recommends running automated tests to identify vulnerabilities and then producing detailed reports that outline medium and high-priority issues with recommended remediation strategies.
To effectively prioritise vulnerabilities, develop a scoring system that considers multiple risk factors. Consider the potential business impact, the sensitivity of affected systems, and the likelihood of exploitation. Create a risk matrix that classifies vulnerabilities into categories such as critical, high, medium, and low priority, ensuring your team focuses on the most significant threats first.
Pro Tip: Implement a dynamic prioritisation approach that considers not just the technical severity, but also the specific context of your organisation’s unique technology ecosystem.
With a clear understanding of your vulnerabilities and their priorities, you are now prepared to develop a targeted remediation strategy.
Step 4: Remediate issues and verify fixes
Remediation is the crucial stage where you transform vulnerability insights into concrete security improvements. Your objective is to systematically address identified risks and confirm that your solutions effectively neutralise potential threats.
NCSC emphasises the importance of promptly remediating vulnerabilities and rigorously verifying that fixes have been implemented successfully. Start by developing a structured remediation plan that prioritises critical vulnerabilities, focusing on patches or configuration changes that directly mitigate the most significant risks. This involves coordinating with your technical team to understand the precise implementation requirements for each identified vulnerability.
After applying remediation strategies, conduct comprehensive verification testing to ensure the fixes have genuinely resolved the underlying security weaknesses. Security.gov.uk recommends carefully analysing any changes to confirm they do not introduce new vulnerabilities while addressing existing ones. Implement a systematic verification process that includes rescanning affected systems, reviewing logs, and performing targeted penetration tests to validate the effectiveness of your remediation efforts.
Pro Tip: Document each remediation step meticulously, creating an audit trail that demonstrates your proactive approach to security management.
With vulnerabilities addressed and fixes verified, you are now prepared to establish ongoing monitoring and continuous improvement practices.
Step 5: Document actions and maintain compliance
Documenting your vulnerability management process is essential for demonstrating organisational diligence and maintaining robust security standards. Your goal in this stage is to create a comprehensive record of all vulnerability management activities that supports both internal accountability and external compliance requirements.
Security.gov.uk emphasises that a clear vulnerability management process allows organisations to maintain confidence in their ability to protect systems and data against emerging threats. Develop a standardised documentation framework that captures critical details including the date of vulnerability discovery, specific system affected, remediation steps taken, verification procedures completed, and the final resolution status. This systematic approach ensures you can track the entire lifecycle of each identified vulnerability.
According to NCSC, maintaining detailed records supports accountability and enables continuous improvement in vulnerability management practices. Create digital repositories that store all vulnerability reports, remediation documentation, and verification evidence. These records should be structured to facilitate easy retrieval during internal audits or when demonstrating compliance with industry standards such as Cyber Essentials or PCI DSS.
Pro Tip: Implement a digital archiving system that automatically timestamps and securely stores all vulnerability management documentation.
With a robust documentation strategy in place, you have established a strong foundation for ongoing cybersecurity management and regulatory compliance.
Take Control of Vulnerability Management for Your SME Today
The challenge of maintaining continuous vulnerability management often overwhelms small and medium-sized businesses. From identifying critical weaknesses and performing regular scans to implementing effective remediation and staying compliant, the process can drain valuable time and resources. This article emphasises the importance of structured vulnerability management steps - like prioritising risks and thorough documentation - to protect your business from evolving cyber threats.
At Freshcyber, we understand these pain points and offer tailored support that makes vulnerability management straightforward and stress free. Our expert team specialises in guiding SMEs through Cyber Essentials and Cyber Essentials Plus certification while delivering seamless ongoing protection. Discover how our proven approach helps you stay compliant all year, not just during audits, with continuous oversight and practical remediation plans.

Ready to secure your SME with expert vulnerability management? Explore our Vulnerability Management solutions designed to keep your systems safe and compliant. Learn more about how we support SME Security and ensure full Compliance. For complete peace of mind and hands-off protection, visit Freshcyber and start your journey towards proactive cybersecurity today.
Frequently Asked Questions
What are the first steps in the vulnerability management process for SMEs?
To effectively manage vulnerabilities, start by assessing your current systems and defining the scope of your vulnerability management process. Conduct a thorough inventory of all digital assets and create a document categorising systems by criticality and potential impact.
How often should SMEs conduct vulnerability scans?
SMEs should aim to conduct vulnerability scans at least once a month or immediately after significant system changes. Implementing a consistent scanning schedule ensures that vulnerabilities are identified and addressed promptly, reducing risk exposure.
How can SMEs prioritise vulnerabilities effectively?
To prioritise vulnerabilities, develop a scoring system that considers factors such as potential business impact, the sensitivity of affected systems, and exploitability. This will help focus your remediation efforts on the most critical threats first.
What steps should be taken after remediating vulnerabilities?
After remediating vulnerabilities, conduct verification testing to ensure that the fixes resolve the issues without introducing new vulnerabilities. Implement a systematic verification process that includes rescanning affected systems and reviewing logs to validate the effectiveness of your remediation efforts.
Why is documentation important in the vulnerability management process?
Documenting your vulnerability management activities is crucial for demonstrating accountability and maintaining compliance with security standards. Create a standardised framework to capture key details about each vulnerability, including remediation steps and verification processes, ensuring easy retrieval for audits.
How can SMEs maintain ongoing compliance and improve their vulnerability management process?
To maintain compliance and improve your vulnerability management process, implement a digital archiving system for all documentation related to vulnerabilities. Regularly review and update your practices to adapt to emerging threats and ensure your approach remains effective.
Recommended
Comments