40% More Contract Wins with UK SME Cyber Compliance
- Gary Sinnott
- 23 hours ago
- 10 min read

Most UK SMEs treat cyber compliance as a bureaucratic burden, a cost centre ticking boxes to satisfy auditors. This perspective wastes one of your firm’s strongest business assets. ISO 27001 certified SMEs experience up to 40% higher contract success rates in compliance-sensitive tenders. The right multi-framework approach transforms compliance into currency, opening doors to high-value contracts and passing enterprise audits that competitors cannot.
Table of Contents
Key Takeaways
Point | Details |
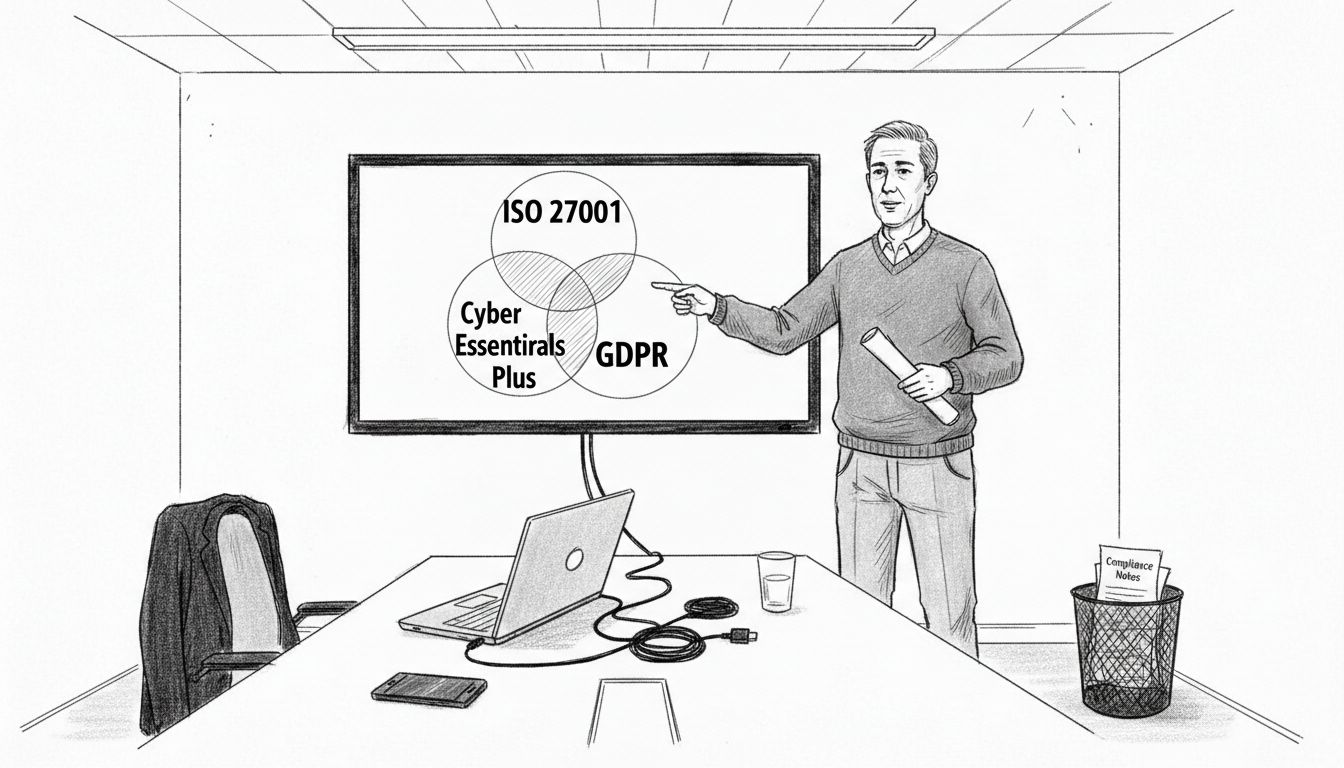
Multi-framework compliance | Combining ISO 27001, Cyber Essentials Plus, and GDPR boosts audit readiness and contract wins. |
vCISO services | Strategic leadership accelerates implementation by 30% while cutting costs by 50% versus traditional consultants. |
24/7 MDR monitoring | Continuous threat detection reduces breach exposure time by 70%, strengthening operational resilience. |
Supply chain security | Third-party vulnerabilities account for 60% of SME cyber breaches, making vendor risk management critical. |
Tailored strategies | Sector-specific compliance approaches balance resource constraints with regulatory and client audit demands. |
How to Choose the Right Cyber Compliance Approach
Selecting the right cyber compliance strategy starts with understanding your sector’s regulatory landscape and client expectations. FinTech firms face stricter data protection scrutiny than e-commerce, while healthcare SMEs must navigate patient data confidentiality alongside general cyber requirements. Your step-by-step cyber compliance guide should align with these realities, not generic checklists.
Multi-framework management offers significant advantages over single-framework approaches. A firm certified only in Cyber Essentials may lose tenders to competitors holding ISO 27001 and GDPR compliance evidence. Combining frameworks demonstrates depth and maturity, signalling to enterprise clients that your security posture can withstand rigorous audits. However, managing multiple standards demands coordination, which is where service model choice becomes critical.
Traditional consultancies charge project-based fees for each framework implementation, creating unpredictable costs that strain SME budgets. A vCISO subscription model bundles multi-framework management under predictable monthly pricing, eliminating surprise invoices when you need policy updates or audit preparation. This approach also provides continuous strategic oversight, ensuring your compliance programme evolves with emerging threats and regulatory changes.
Cost and resource limitations force tough choices. A lean compliance team cannot dedicate staff to full-time framework maintenance without sacrificing core business operations. Safeguarding UK business integrity requires balancing immediate audit needs with long-term scalability, which means prioritising frameworks that deliver the highest ROI in contract wins and client confidence.
Audit readiness separates winning bids from rejected proposals. Enterprise clients increasingly conduct pre-contract security assessments, and firms unable to prepare for cyber audits lose opportunities regardless of technical capability. Your compliance approach must produce audit-ready documentation, risk registers, and policy suites that pass scrutiny without last-minute scrambling.
Pro Tip: Map your top three target clients’ compliance requirements before selecting frameworks. If two require ISO 27001 and one accepts Cyber Essentials Plus, prioritise ISO to maximise contract eligibility.
Multi-Framework Compliance: ISO 27001, Cyber Essentials Plus, and GDPR
ISO 27001:2022 represents the gold standard for information security management systems in the UK. This framework requires comprehensive risk assessment, policy documentation, and continuous improvement cycles that demonstrate mature security governance. ISO 27001 certified SMEs experience up to 40% higher contract success rates because large organisations trust the standard’s rigour and global recognition.
Cyber Essentials Plus provides government-backed certification focused on technical controls protecting against common threats. The certification involves external vulnerability testing and configuration checks, offering tangible evidence of baseline security hygiene. Many public sector contracts mandate Cyber Essentials as a minimum threshold, making it essential for firms bidding on government work.
GDPR compliance governs data protection and privacy obligations for any organisation processing personal information of UK or EU residents. While not a certification, GDPR requires documented processes, data protection impact assessments, and breach notification procedures. Non-compliance risks fines up to 4% of annual turnover, but demonstrable GDPR alignment also strengthens client trust and contract viability.
Framework | Scope | Audit Benefit | Typical Cost | Key Impact |
ISO 27001:2022 | Full ISMS lifecycle | High credibility in enterprise tenders | £15k-£40k initial | 40% higher contract success |
Cyber Essentials Plus | Technical controls and vulnerability testing | Government contract eligibility | £3k-£5k annually | Public sector access |
GDPR Compliance | Data protection and privacy management | Legal obligation and client confidence | £5k-£15k setup | Avoids 4% turnover fines |
Combining these frameworks creates layered compliance that addresses both strategic governance and tactical security. ISO 27001 in business establishes the management system foundation, while Cyber Essentials Plus explained adds verified technical assurance. GDPR integration ensures data handling meets legal and ethical standards, a critical differentiator in healthcare and financial services.
The ISO/IEC 27001 official guidance emphasises continuous improvement and risk-based thinking. This approach means your compliance programme adapts to new threats and business changes, maintaining relevance beyond initial certification. Stale compliance documentation fails audits and undermines the commercial value of your investment.
Pro Tip: Prioritise frameworks based on your client base. If 70% of your revenue comes from private sector enterprises, invest in ISO 27001 before Cyber Essentials to match buyer expectations.
vCISO-Led Compliance Management: Strategic Leadership for SMEs
A virtual Chief Information Security Officer provides executive-level security leadership without the £120k+ salary of a full-time hire. vCISO services deliver strategic oversight across framework implementation, risk management, and policy governance, ensuring your compliance programme aligns with business objectives rather than existing in isolation.
Cost savings average 50% compared to traditional consultancy models because vCISO subscriptions bundle gap analysis, Statement of Applicability development, audit preparation, and ongoing policy updates under fixed monthly fees. This eliminates the consultancy practice of charging separately for each deliverable, a model that inflates costs as your compliance needs expand.
Implementation timelines accelerate by approximately 30% under vCISO guidance. A dedicated security executive knows the fastest path through certification requirements, avoiding the trial-and-error delays common when internal teams manage compliance part-time. Faster implementation means earlier access to contract opportunities and quicker ROI on compliance investment.
Virtual CISO services integrate risk registers, policy libraries, and audit management into a cohesive security roadmap. Your vCISO maintains dynamic documentation that reflects current business operations, not outdated templates. This living compliance posture passes audits and adapts to regulatory changes without requiring complete programme overhauls.
Strategic risk management separates vCISO leadership from basic compliance support. A vCISO identifies security investments that protect business value, not just those that satisfy auditors. This includes prioritising controls that reduce cyber insurance premiums, strengthen vendor relationships, and enhance brand reputation alongside certification requirements.
Full lifecycle ISMS development from gap analysis to certification maintenance
Bespoke policy suites tailored to your sector and operational reality
Dynamic risk registers linking security controls to business impact
Audit liaison and evidence preparation reducing internal workload
Strategic advice on security investments maximising commercial value
Pro Tip: Evaluate vCISO providers on their multi-framework expertise. A specialist handling only ISO 27001 cannot optimise your compliance portfolio across Cyber Essentials Plus and GDPR simultaneously.
Real-world outcomes demonstrate vCISO impact. SMEs report passing client audits that previously resulted in contract losses, gaining access to enterprise procurement processes that exclude non-certified suppliers, and reducing cyber insurance premiums through demonstrable risk reduction. The cybersecurity compliance workflow under vCISO leadership transforms compliance from administrative overhead into competitive advantage.
Active Defence: 24/7 Monitoring and Managed Detection and Response (MDR)
Continuous threat monitoring transforms compliance from static certification into dynamic protection. 70% reduction in exposure time to cyber threats with 24/7 MDR deployment occurs because automated detection spots anomalies within minutes rather than the weeks typical of manual review cycles. Faster detection limits damage and demonstrates to auditors that your security controls actively function.
Managed detection and response services monitor Microsoft 365, Google Workspace, AWS, and internal networks for indicators of compromise. This comprehensive visibility spans cloud applications, email systems, and infrastructure, ensuring no blind spots where threats hide undetected. Enterprise clients increasingly require evidence of monitoring capabilities during pre-contract security reviews.
Perimeter intelligence and vulnerability scanning identify weaknesses before attackers exploit them. Automated penetration testing runs continuously, flagging misconfigurations and unpatched systems that create exposure. Vulnerability management integrates with compliance frameworks, providing audit evidence that you proactively maintain security hygiene.
Incident isolation and containment capabilities distinguish MDR from basic monitoring. When threats emerge, MDR teams execute predefined response procedures, quarantining affected systems and preventing lateral movement. This rapid containment protects business continuity and demonstrates resilience to clients evaluating your risk profile.
Real-time alerting on suspicious authentication attempts and data access patterns
Automated threat intelligence correlation identifying emerging attack techniques
Incident response playbooks executed by security operations centres
Forensic analysis and root cause investigation after security events
Business continuity support ensuring operational recovery post-incident
MDR Impact: SMEs using 24/7 monitoring detect breaches in hours versus the industry average of 207 days, limiting financial damage and reputational harm.
Integrating MDR with ISO 27001 and Cyber Essentials Plus creates holistic security posture. Compliance frameworks define what controls you implement, while MDR proves those controls function effectively. Auditors increasingly request monitoring logs and incident response evidence, making MDR benefits essential for certification maintenance and client confidence.
Supply Chain Security and Audit Readiness
60% of SME cyber breaches in the UK linked to third-party vendor vulnerabilities demonstrates why supply chain security cannot remain an afterthought. Your compliance status means nothing if a supplier’s weak security provides attackers a backdoor into your systems. Enterprise clients recognise this risk, making vendor risk management a standard audit checkpoint.
Initial third-party risk assessments should evaluate potential suppliers before contract signing. Request security certifications, review their incident history, and assess whether their compliance posture matches your own standards. A supplier lacking ISO 27001 when you hold certification creates risk asymmetry that auditors flag and clients question.
Continuous monitoring extends beyond initial vetting. Annual reassessments verify that supplier security postures remain robust as their operations evolve. Automated vendor risk platforms track certification expiries and breach disclosures, alerting you to deteriorating risk profiles before they impact your operations.
Documenting compliance readiness requires maintaining audit trails that demonstrate ongoing vendor oversight. Your risk register should list all suppliers handling sensitive data, document their security controls, and record assessment results. This evidence satisfies client audits and proves your supply chain governance operates systematically, not reactively.
Inventory all third parties with access to your systems or data
Classify suppliers by risk level based on data access and business criticality
Conduct initial security assessments using standardised questionnaires
Review certifications and request audit reports for high-risk vendors
Establish contractual security requirements and incident notification obligations
Schedule annual reassessments and track certification renewals
Maintain centralised vendor risk register accessible during client audits
Vendor Risk Level | Assessment Frequency | Required Evidence | Contract Clause |
Critical (data processors) | Quarterly | ISO 27001, SOC 2, penetration test results | Right to audit, breach notification within 24 hours |
High (system access) | Semi-annually | Cyber Essentials Plus, GDPR compliance documentation | Security incident reporting, annual reviews |
Medium (limited access) | Annually | Basic security questionnaire, insurance certificate | Standard security terms |
Low (no data access) | Bi-annually | General liability insurance | Minimal security requirements |
Strong compliance status strengthens vendor partnerships by demonstrating your firm meets the same standards you demand from suppliers. Prepare for cyber audits by treating your own organisation as you would a critical supplier, maintaining the documentation and controls that satisfy rigorous external review.
Security audits for UK SMEs increasingly focus on supply chain governance because breaches originating from vendors trigger the same regulatory penalties and reputational damage as internal incidents. Your vendor risk management programme protects both your operations and your market credibility.
Pro Tip: Include security requirements in procurement contracts before vendor selection. Retrofitting security clauses after contract signing creates friction and weakens your negotiating position.
The NCSC supply chain security guidance provides detailed frameworks for assessing and managing third-party risk. Following NCSC recommendations demonstrates to auditors that your supply chain programme aligns with national security standards, strengthening your compliance evidence portfolio.
Enhance Your SME Cyber Compliance with Expert Solutions
Transforming compliance into competitive advantage requires expertise, strategic vision, and operational execution that most SMEs cannot resource internally. Freshcyber specialises in turning cyber frameworks into business assets for UK firms in FinTech, healthcare, and e-commerce seeking to secure high-value contracts and pass rigorous audits.

Our vCISO-led Compliance Currency Engine manages ISO 27001, Cyber Essentials Plus, and GDPR under a single subscription, eliminating the consultancy tax that inflates costs with each new project. We take full ownership of your security roadmap, from gap analysis through certification and ongoing compliance maintenance.
24/7 MDR services provide the operational muscle protecting the compliance foundation we build. Real-time threat monitoring across Microsoft 365, AWS, and Google Workspace ensures your security controls actively function, not just exist on paper. Our cybersecurity services for UK SMEs integrate strategic leadership with tactical defense, creating resilience that wins contracts and passes audits.
Discover how vCISO services accelerate your compliance journey while our managed detection and response solutions protect what you build. Compliance becomes currency when expert execution transforms security into your strongest sales asset.
Frequently Asked Questions
How can SMEs balance budget constraints with comprehensive cyber compliance?
Subscription-based vCISO services reduce compliance costs by approximately 50% compared to traditional consultancies by bundling multi-framework management under predictable monthly fees. This model eliminates surprise invoicing for audit preparation, policy updates, and certification maintenance.
ROI emerges through reduced audit failures and breach costs. Firms with robust compliance avoid contract losses from failed security reviews and benefit from lower cyber insurance premiums due to demonstrable risk reduction. The cost of compliance becomes minimal compared to lost revenue opportunities.
What are the biggest pitfalls UK SMEs face in cyber compliance?
Treating compliance as a one-time project rather than ongoing governance creates stale documentation that fails audits and provides no real protection. Certifications require continuous maintenance, policy updates, and risk register reviews to remain valid and valuable.
Neglecting supply chain risk leaves backdoors open despite strong internal controls. With 60% of breaches linked to third-party vulnerabilities, ignoring vendor security undermines your entire compliance investment. Dynamic risk management must extend beyond your organisation’s boundaries.
How does compliance help SMEs win high-value contracts?
Certifications like ISO 27001 serve as tender differentiators, with certified firms experiencing 40% higher contract success rates in compliance-sensitive procurement. Enterprise buyers use security standards as initial filters, eliminating non-certified suppliers before evaluating technical capability or pricing.
Audit readiness accelerates sales cycles by satisfying pre-contract security reviews without delays. Firms with comprehensive compliance documentation close deals faster because buyers can verify security posture immediately, reducing procurement friction and competitive risk.
Recommended