Security Posture - Turning Compliance into Advantage
- Gary Sinnott

- Feb 8
- 7 min read

For many British IT leaders, the pressure of meeting compliance mandates like ISO 27001 and Cyber Essentials often misleads organisations into thinking that tick-box certification guarantees real security. The truth is, a strong security posture demands more than technology alone - it relies on smart processes and skilled people to handle threats that evolve faster than any checklist can keep up with. This guide offers practical insights to help you challenge common myths, avoid costly pitfalls, and strengthen your cyber resilience with actionable, sector-relevant strategies.
Table of Contents
Key Takeaways
Point | Details |
Importance of Security Posture | A comprehensive security posture involves people, processes, and technology, and should be viewed as a strategic business function rather than just a technical necessity. |
Dynamic Strategies Required | Effective security strategies must be adaptive and regularly assessed to address emerging threats, moving beyond static implementations. |
Compliance as a Continuous Process | Security posture improvements should integrate compliance standards as part of a dynamic framework rather than treating them as mere checklists. |
Proactive Risk Management | Organisations should adopt proactive and continuous validation strategies to anticipate and mitigate potential security threats effectively. |
Defining Security Posture and Common Myths
A security posture represents an organisation’s comprehensive approach to managing cybersecurity risks, extending far beyond simple technological interventions. Comprehensive risk assessment strategies reveal that security posture encompasses multiple interconnected dimensions that protect an organisation’s digital infrastructure.
At its core, security posture involves three critical elements:
People: Human capabilities, training, and awareness
Processes: Systematic approaches to identifying and mitigating risks
Technology: Specific tools and infrastructure used for protection
Many organisations harbour misconceptions about what constitutes an effective security strategy. Common myths include believing that compliance automatically guarantees security or that technological solutions alone can protect against sophisticated cyber threats. Cloud security challenges demonstrate that a holistic approach is necessary, integrating technical controls with robust governance frameworks.
The most effective security postures are dynamic and adaptive, continuously evolving to address emerging threats. They require regular assessment, gap analysis, and proactive management rather than static, checkbox-style implementations. Organisations must view security as a strategic business function, not merely a technical requirement.
Pro tip: Conduct quarterly comprehensive security assessments to maintain a resilient and responsive security posture.
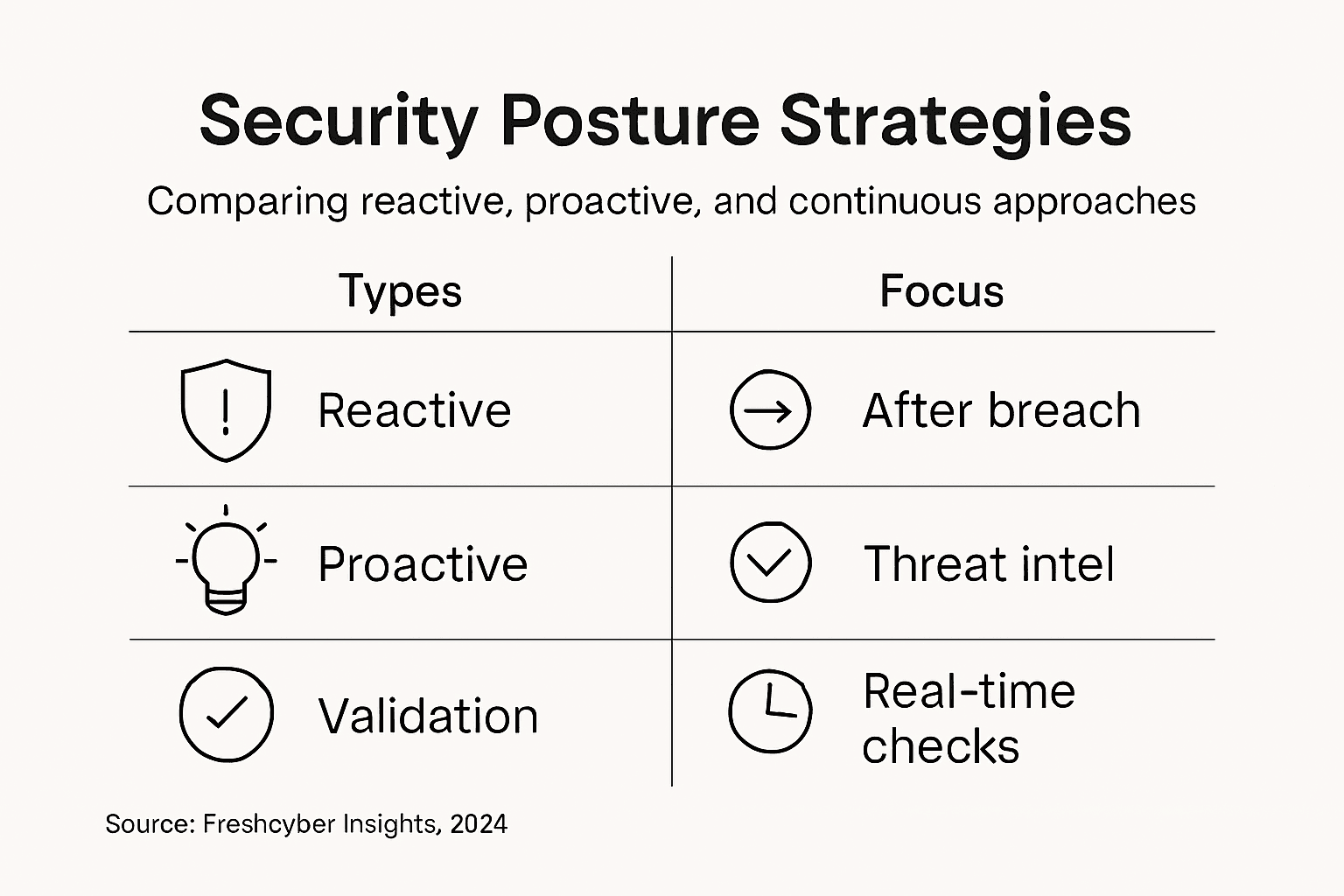
Different Types of Security Posture Strategies
Organisations can adopt multiple strategic approaches to managing their cybersecurity risk, each with distinct characteristics and objectives. Emerging security posture management strategies reveal three primary models that define how businesses protect their digital assets.
The primary security posture strategies include:
Reactive Strategy: Responding to incidents after they occur
Proactive Strategy: Anticipating and preventing potential security threats
Continuous Validation Strategy: Ongoing assessment and real-time monitoring of security controls
In a reactive strategy, organisations primarily focus on addressing security breaches after they have happened. This approach involves incident response, forensic analysis, and post-event mitigation. While necessary, it leaves businesses vulnerable to significant potential damage and financial losses.
The proactive strategy represents a more sophisticated approach. It involves predictive threat intelligence, regular vulnerability assessments, and preemptive security measures. Proactive organisations invest in advanced behavioural analytics, threat hunting, and automated risk prioritisation to identify and neutralise potential security risks before they escalate.
Continuous validation strategies represent the most advanced security posture model. These approaches leverage real-time monitoring, automated testing, and dynamic risk assessment to maintain an adaptive and resilient security environment. By continuously validating security controls and rapidly responding to emerging threats, organisations can maintain a robust defence mechanism.
The following table compares key security posture strategies and their organisational implications:
Strategy Type | Main Focus | Strengths | Limitations |
Reactive | Incident response | Essential for damage control | Only acts after breach |
Proactive | Threat prevention | Prevents many incidents | May miss unknown attacks |
Continuous Validation | Ongoing monitoring and testing | Rapid adaption to new risks | Requires ongoing resources |
Pro tip: Implement a hybrid security strategy that combines elements of proactive and continuous validation approaches to maximise your organisational resilience.
Key Components: People, Processes, Technology
A robust security posture is fundamentally built upon three interdependent pillars: people, processes, and technology. These components work synergistically to create a comprehensive defence mechanism that protects an organisation’s digital assets and mitigates potential cyber risks.
The people component encompasses several critical elements:
Security awareness training
Cultural understanding of cybersecurity
Individual skill development
Role-specific security responsibilities
Continuous learning and adaptation
The processes dimension represents the systematic approaches and frameworks that guide an organisation’s security strategy. This includes establishing clear protocols for:
Risk assessment procedures
Incident response workflows
Compliance management
Regular security audits
Third-party vendor risk evaluation
The technology element involves the actual tools, systems, and infrastructure used to implement and enforce security measures. Modern technological components include:
Endpoint protection systems
Network monitoring tools
Multi-factor authentication platforms
Encryption technologies
Security information and event management (SIEM) solutions
Successful security postures recognise that these three components are not isolated, but deeply interconnected. Technology without skilled people and robust processes becomes ineffective, while processes without supporting technology cannot be efficiently implemented. The most resilient organisations create a holistic approach that integrates these elements seamlessly.
Pro tip: Conduct an annual comprehensive review that evaluates the interaction between your people, processes, and technology to identify potential improvement areas.
Compliance Standards Impacting Security Posture
Comprehensive security posture cannot be achieved without understanding and implementing critical compliance standards that guide organisational cybersecurity practices. UK cyber security codes of practice provide essential frameworks for businesses seeking to establish robust digital defences.
The most significant compliance standards impacting security posture include:
Cyber Essentials
ISO 27001
GDPR
NCSC Cyber Assessment Framework
PCI DSS
The Cyber Essentials standard, developed by the National Cyber Security Centre, represents a fundamental baseline for organisational cybersecurity. This framework focuses on five key control areas that help businesses protect against common cyber threats, including:
Boundary firewalls and internet gateways
Secure configuration
User access control
Malware protection
Patch management
ISO 27001 provides a more comprehensive approach to information security management. Unlike basic compliance checklists, this international standard requires organisations to develop a systematic approach to managing sensitive information, ensuring its confidentiality, integrity, and availability.
National cyber security guidance emphasises that compliance is not a one-time achievement but a continuous process of assessment, improvement, and adaptation. The most effective security postures integrate these standards dynamically, treating them as strategic frameworks rather than mere bureaucratic requirements.
Here is a summary of major compliance standards and their core organisational benefits:
Compliance Standard | Primary Focus Area | Organisational Benefit |
Cyber Essentials | Basic technical controls | Eases vendor trust and baseline security |
ISO 27001 | Information security management | Global recognition and risk reduction |
GDPR | Personal data protection | Avoids fines and builds customer trust |
NCSC CAF | Risk and resilience frameworks | Aligns with UK government expectations |
PCI DSS | Payment data security | Reduces liability in card transactions |
Pro tip: Conduct a gap analysis against multiple compliance standards annually to identify and address potential security vulnerabilities.
Risks, Liabilities, and Improvement Pitfalls
Cybersecurity risks are rapidly evolving, presenting complex challenges for organisations seeking to maintain a robust security posture. Global cybersecurity risks highlight the increasing sophistication of threats that can potentially devastate unprepared businesses.
The most significant risks and potential liabilities include:
Financial losses from data breaches
Regulatory non-compliance penalties
Reputational damage
Operational disruption
Legal liability for customer data protection
Technological vulnerabilities create multiple potential pitfalls for organisations attempting to improve their security posture. Common improvement challenges include:
Underestimating emerging cyber threats
Insufficient risk assessment methodologies
Limited staff cybersecurity training
Fragmented security infrastructure
Reactive instead of proactive security approaches
Systematic security posture assessments reveal that many organisations struggle with comprehensive risk management. Supply chain attacks, ransomware, and insider threats represent particularly insidious risks that exploit organisational blind spots, potentially causing catastrophic operational and financial consequences.
Successful risk mitigation requires a holistic, adaptive approach that continuously evaluates and updates security strategies. Organisations must move beyond checkbox compliance and develop dynamic, intelligence-driven security frameworks that anticipate and neutralise emerging threats.
Pro tip: Implement a quarterly threat intelligence review to proactively identify and address potential security vulnerabilities before they can be exploited.
Elevate Your Security Posture from Compliance to Competitive Advantage
Understanding the complexities of security posture means recognising the need for more than just ticking compliance boxes. This article highlights your challenge: transforming compliance into a strategic asset that drives business resilience and growth. You face pressure managing intertwined elements of people, processes, and technology while navigating multiple standards like ISO 27001 and Cyber Essentials. Without expert leadership and continuous monitoring, vulnerabilities and risks can quickly escalate.
Freshcyber offers a tailored solution designed specifically for SMEs looking to build a dynamic, proactive, and continuously validated security posture. Our Compliance expertise - with flagship vCISO-led services - helps you implement comprehensive frameworks and maintain a living Risk Register that protects your firm’s value. Complement this with 24/7 active defence through our Vulnerability Management capabilities to stay ahead of threats. By choosing Freshcyber, you turn compliance into currency that wins contracts and powers future growth.
Are you ready to go beyond basic security and make compliance your strongest sales asset?

Visit Freshcyber today and partner with us to transform your security posture into a resilient business advantage.
Frequently Asked Questions
What is security posture in cybersecurity?
Security posture refers to an organisation’s overall strategy and readiness to manage cybersecurity risks. It includes the combination of people, processes, and technology to protect digital assets from potential threats.
How can compliance standards improve my organisation’s security posture?
Compliance standards provide frameworks that guide organisations in implementing effective security practices. They help identify vulnerabilities, enforce cybersecurity measures, and ensure a systematic approach to protecting sensitive information.
What are the key components of a strong security posture?
A strong security posture is built upon three interdependent components: people, processes, and technology. These elements work together to create a comprehensive defence mechanism against cyber threats.
What is the difference between reactive and proactive security posture strategies?
A reactive security posture focuses on responding to incidents after they occur, while a proactive strategy involves anticipating and preventing potential threats. Proactive strategies aim to identify vulnerabilities before they can be exploited.
Recommended
Comments