ISO 27001 Certification Explained: Key Steps and Benefits
- Gary Sinnott

- Nov 24, 2025
- 6 min read

Over 80% of British businesses have reported cyber attacks in the past year. Keeping sensitive information safe has become more than a priority - it is a necessity. ISO 27001 certification stands out as a powerful tool, helping organisations create a systematic, proven approach to information security. This guide offers clear insights into how this internationally recognised standard works, why it matters for British companies, and what steps are involved for those seeking real data protection and lasting peace of mind.
Table of Contents
Key Takeaways
Point | Details |
ISO 27001 Certification | Offers a comprehensive framework for managing information security, focusing on confidentiality, integrity, and availability of data. |
Core Requirements | Emphasises a holistic approach covering risk assessment, policy development, and operational security, tailored to organisational needs. |
Certification Process | Involves multiple stages including risk assessment, control implementation, and external audits, requiring ongoing commitment to security vigilance. |
Continuous Improvement | Mandates regular audits and updates to security protocols, creating a proactive culture that adapts to emerging threats. |
What Is ISO 27001 Certification?
ISO 27001 certification represents a robust international standard for managing information security within organisations. According to iso.org, this framework provides a systematic approach to protecting sensitive company information, ensuring its confidentiality, integrity, and availability.
At its core, ISO 27001 is an information security management system (ISMS) that helps businesses establish comprehensive protocols for identifying, managing, and minimising information security risks. The certification goes beyond simple technical controls, requiring organisations to develop a holistic strategy that encompasses people, processes, and technology. This means creating structured policies, conducting regular risk assessments, and implementing continuous improvement mechanisms that adapt to evolving cyber threats.
The certification process involves several critical stages, including:
Conducting a thorough information security risk assessment
Developing detailed security policies and procedures
Implementing robust technical and organisational controls
Undertaking regular internal audits
Demonstrating compliance through external certification
By pursuing ISO 27001 certification, businesses signal their commitment to protecting critical data assets. This approach not only mitigates potential security vulnerabilities but also builds significant trust with clients, partners, and stakeholders who increasingly demand rigorous information protection standards.
Core Requirements and Control Areas
iso.org specifies that ISO 27001 establishes comprehensive requirements for creating and maintaining an Information Security Management System (ISMS). The standard provides a structured framework that goes far beyond simple technical safeguards, demanding a holistic approach to information protection across an organisation’s entire operational landscape.
The core requirements are organised into several critical control areas, which encompass both strategic and tactical dimensions of information security. These include:
Risk Assessment: Systematic identification and evaluation of potential information security threats
Policy Development: Creating comprehensive security policies tailored to organisational needs
Asset Management: Identifying and classifying information assets with appropriate protection mechanisms
Access Control: Implementing robust user authentication and authorisation protocols
Cryptography: Deploying encryption technologies to protect sensitive data
Physical and Environmental Security: Protecting physical infrastructure and computing environments
Operational Security: Establishing secure operational procedures and incident management processes
Each control area requires meticulous documentation, regular review, and continuous improvement. Organisations must demonstrate not just the existence of these controls, but also their effective implementation and ongoing management.
This means developing clear procedures, training staff, conducting regular audits, and maintaining comprehensive records that prove compliance.
The real power of ISO 27001 lies in its adaptability. Unlike rigid security frameworks, this standard recognises that each organisation has unique risk profiles and operational contexts. By mandating a risk-based approach, businesses can develop security strategies that are both comprehensive and precisely tailored to their specific needs, ensuring that resources are allocated efficiently and vulnerabilities are addressed strategically.
The ISO 27001 Certification Process
According to iso.org, the ISO 27001 certification process encompasses a comprehensive journey through multiple strategic stages designed to transform an organisation’s approach to information security. The certification is not a one-time achievement, but a continuous commitment to maintaining robust security protocols and evolving with emerging technological challenges.
The certification journey typically involves six critical stages:
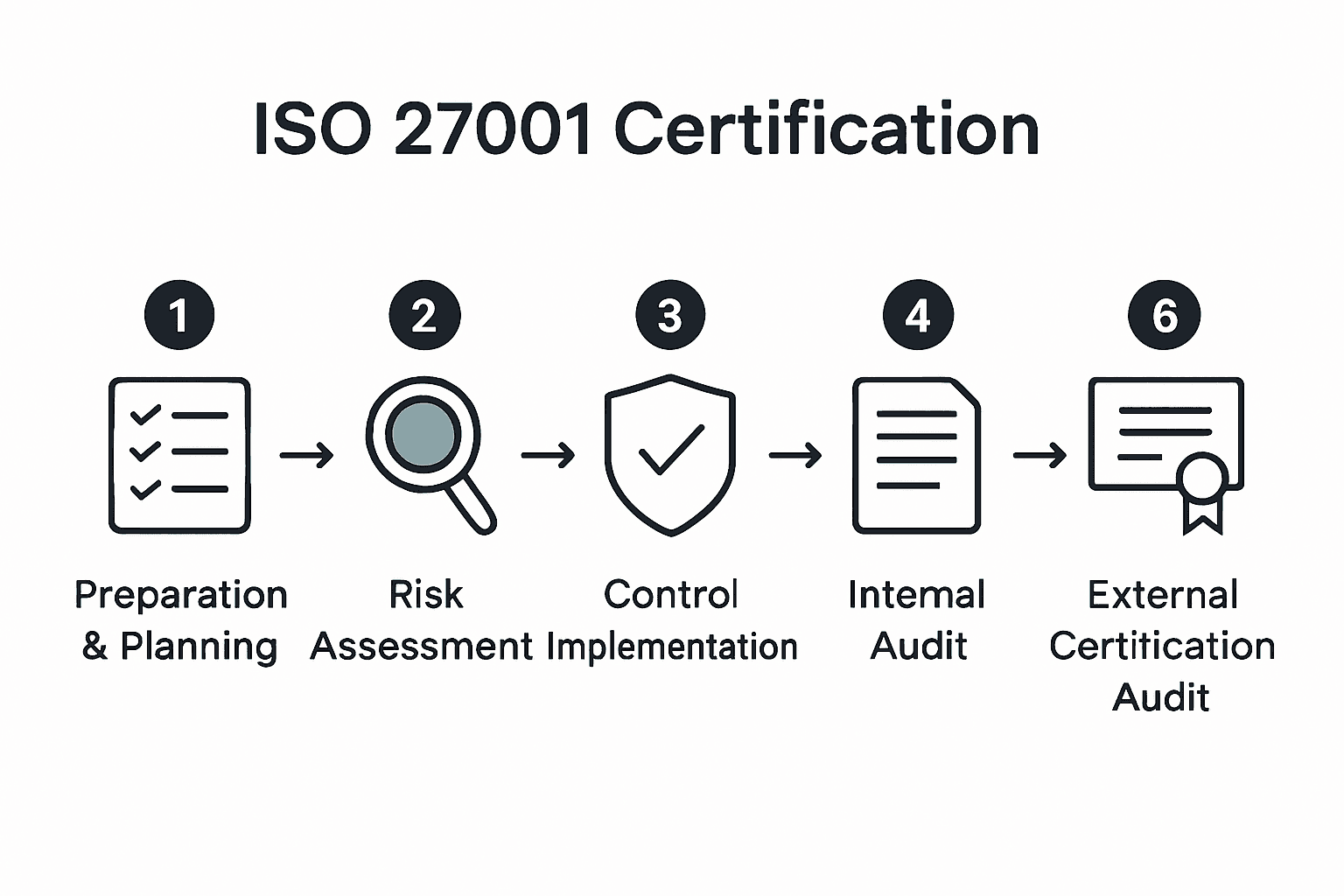
Preparation and Planning: Establishing initial security management framework
Risk Assessment: Conducting thorough identification and evaluation of potential information security risks
Control Implementation: Developing and deploying specific security measures addressing identified vulnerabilities
Internal Audit: Performing comprehensive internal review to validate implemented controls
Management Review: Senior leadership assessment of the Information Security Management System (ISMS)
External Certification Audit: A two-stage external evaluation by an accredited certification body
Each stage demands meticulous attention and documented evidence. Organisations must demonstrate not just the existence of security controls, but their consistent, effective implementation. This means creating detailed documentation, training personnel, establishing clear procedures, and maintaining a culture of continuous improvement.
For businesses seeking ISO 27001 in Business: Complete Compliance Guide, the process represents more than a compliance checkbox. It’s a strategic approach to transforming information security from a technical requirement into a core organisational capability. Successful certification signals to clients, partners, and stakeholders that the organisation takes data protection seriously, building trust and demonstrating a proactive approach to managing digital risks.
Costs, Benefits, and Common Challenges
According to Forbes, ISO 27001 certification involves significant investment, with expenses spanning implementation, training, and comprehensive audit processes. While the financial commitment can seem substantial, the strategic returns far outweigh the initial costs for organisations committed to robust information security.
The key benefits of ISO 27001 certification include:
Enhanced Information Security: Systematic approach to identifying and mitigating digital risks
Regulatory Compliance: Demonstrating adherence to international security standards
Customer Trust: Proving commitment to protecting sensitive organisational and client data
Competitive Advantage: Differentiating from competitors through proven security frameworks
Reduced Operational Risks: Minimising potential financial and reputational damage from security breaches
Deloitte highlights that organisations typically encounter several challenges during certification, including complex resource allocation, comprehensive employee training, and seamlessly integrating the Information Security Management System (ISMS) into existing organisational processes. These challenges require dedicated leadership commitment, strategic planning, and a cultural shift towards prioritising information security.
Ultimately, ISO 27001 certification is not merely an expense but a strategic investment. By proactively addressing potential vulnerabilities, organisations can transform information security from a compliance requirement into a powerful business enabler, building stakeholder confidence and creating a resilient foundation for digital operations.
Maintaining Compliance and Continuous Improvement
According to iso.org, maintaining ISO 27001 compliance is not a one-time achievement but a dynamic, ongoing process requiring consistent vigilance and proactive management. The standard mandates regular internal audits, comprehensive management reviews, and continuous monitoring to ensure the Information Security Management System (ISMS) remains robust and adaptive in the face of evolving digital threats.
Key strategies for maintaining compliance include:
Regular Risk Assessments: Conducting periodic evaluations of potential security vulnerabilities
Internal Audits: Systematically reviewing and validating existing security controls
Management Reviews: Ensuring senior leadership actively oversees and updates security protocols
Employee Training: Continuously educating staff about emerging security risks and best practices
Documentation Updates: Maintaining current and comprehensive security documentation
Technology Monitoring: Tracking and integrating latest security technologies and methodologies
Continuous improvement requires organisations to develop a dynamic, responsive approach to information security. This means creating a culture of proactive risk management, where security is not viewed as a static checklist but as an evolving strategic capability. Complete Guide to Decoding the Cyber Audit Process can provide additional insights into maintaining this strategic approach.
Successful long-term compliance demands more than technical controls. It requires cultivating an organisational mindset that prioritises security, encourages ongoing learning, and remains agile in responding to new technological challenges. By embracing this philosophy, businesses can transform ISO 27001 certification from a regulatory requirement into a powerful competitive advantage.
Secure Your Path to ISO 27001 Certification with Expert Support
Achieving ISO 27001 certification demands a clear strategy, thorough risk assessment, and continuous security management. Many organisations face challenges such as maintaining comprehensive documentation, conducting regular audits, and integrating information security into daily operations. If you want to overcome these hurdles and build lasting trust with clients, you need practical, expert guidance tailored to your business needs.
Freshcyber specialises in simplifying compliance journeys with our Compliance and Vulnerability Management services. We help busy business owners and IT teams maintain robust security frameworks that align perfectly with ISO 27001 requirements while avoiding last-minute stress or surprises.

Take control of your information security management now. Visit Freshcyber to discover how our comprehensive support can transform your certification process into a seamless, confident experience.
Frequently Asked Questions
What is ISO 27001 certification?
ISO 27001 certification is an international standard that provides a systematic approach to managing information security risks, ensuring the confidentiality, integrity, and availability of sensitive data within organisations.
What are the key steps in the ISO 27001 certification process?
The key steps in the ISO 27001 certification process include preparation and planning, risk assessment, control implementation, internal audit, management review, and external certification audit.
What are the main benefits of obtaining ISO 27001 certification?
The main benefits of ISO 27001 certification include enhanced information security, regulatory compliance, increased customer trust, competitive advantage, and reduced operational risks associated with data breaches.
How can organisations maintain compliance with ISO 27001?
Organisations can maintain compliance with ISO 27001 by conducting regular risk assessments, performing internal audits, ensuring management reviews, providing ongoing employee training, updating documentation, and monitoring new security technologies.
Recommended
Comments