Cyber Security Certification Guide for UK SMEs
- Gary Sinnott

- Nov 27, 2025
- 8 min read

A staggering 69 percent of British small and medium enterprises operate without a formal cybersecurity policy, leaving them exposed to growing digital threats. As cyber attacks become more frequent and complex, businesses across the UK face mounting pressure to secure sensitive data and comply with strict industry regulations. Whether you are just beginning your cyber journey or seeking to strengthen your defences, understanding each key step in the cyber certification process can give your organisation the security and credibility it needs.
Table of Contents
Quick Summary
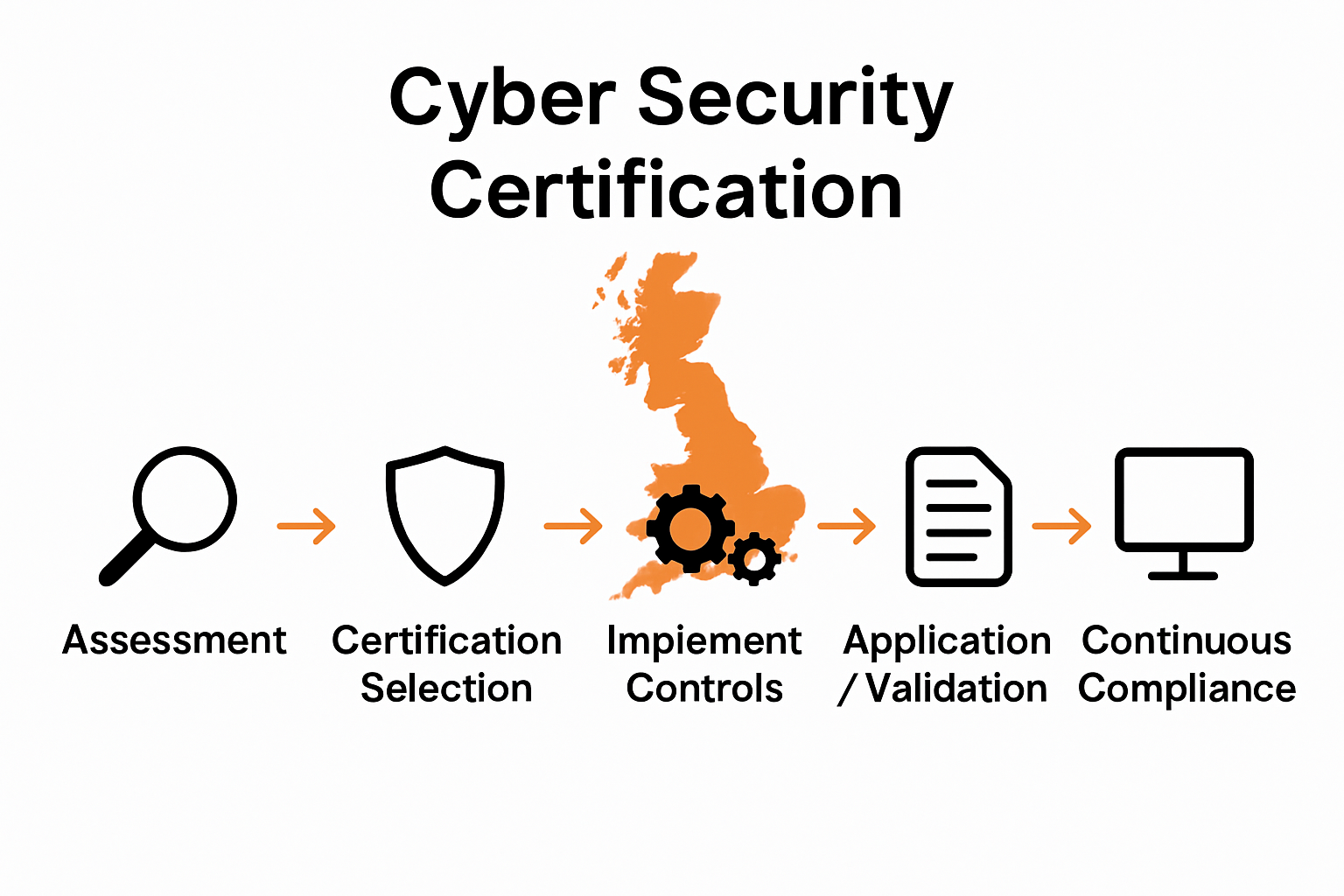
Key Insight | Explanation |
1. Assess current security needs | Conduct a thorough evaluation of existing security practices to identify vulnerabilities and regulatory requirements. |
2. Choose suitable certification | Select the right cybersecurity certification based on industry needs, organisational maturity, and budget. |
3. Implement essential controls | Establish key security measures such as firewalls, access control, and malware protection to enhance cyber defences. |
4. Adjust to compliance processes | Treat the certification application as an opportunity to demonstrate commitment, ensuring thorough documentation of security practices. |
5. Maintain continuous monitoring | Adopt ongoing monitoring and assessment strategies to proactively identify and address security vulnerabilities. |
Step 1: Assess current security and compliance requirements
Assessing your organisation’s current security and compliance requirements is the critical first step in achieving robust cyber protection. This process involves conducting a comprehensive review of your existing security practices, identifying potential vulnerabilities, and understanding the specific regulatory standards that apply to your business.
According to Ramsac, a staggering 69% of UK SMEs currently lack a formal cybersecurity policy. This statistic underscores the importance of establishing clear, concise policies that cover critical areas such as acceptable device usage, password management, data handling procedures, and incident reporting protocols. Start by mapping out your current security landscape by examining:
Existing IT infrastructure and network configurations
Current security tools and software in use
Employee access levels and authentication mechanisms
Data storage and transmission practices
Incident response and recovery capabilities
The UK Government Security website recommends creating a Security Obligations Matrix to track various regulatory requirements. This matrix should include laws, regulations, accreditations, government policies, and third-party contractual obligations specific to your industry.
Pro tip: Do not view this assessment as a one-time activity. Treat it as an ongoing process that requires regular review and updating to stay ahead of emerging cyber threats and evolving compliance standards.
Once you have completed this comprehensive assessment, you will have a clear baseline of your current security posture and a roadmap for targeted improvements and certification preparation.
Step 2: Select the appropriate certification scheme
Choosing the right certification scheme is a strategic decision that will shape your organisation’s cybersecurity approach and demonstrate your commitment to robust digital protection. This step involves carefully evaluating different certification options to find the most suitable framework for your business needs and industry requirements.
The National Cyber Security Centre recommends Cyber Essentials as the minimum standard of cybersecurity for UK organisations. This certification scheme offers two distinct levels to match varying business complexity and security maturity. The basic Cyber Essentials provides a verified self-assessment approach, while Cyber Essentials Plus involves an independent technical verification process.
When selecting your certification scheme, consider the following key factors:
Your industry sector and specific regulatory requirements
Current level of cybersecurity maturity
Complexity of your IT infrastructure
Budget and resources available for certification
Potential client or contractual security expectations
For many small and medium enterprises, the Cyber Essentials framework offers an excellent starting point. It covers fundamental security controls and helps businesses protect against common cyber threats. If you operate in sectors handling sensitive data such as finance, healthcare, or professional services, you might need to explore more comprehensive certifications like Cyber Essentials Plus, and ISO 27001.
Pro tip: Do not view certification as a mere compliance checkbox. Treat it as an opportunity to genuinely enhance your organisation’s security posture and build trust with clients and partners.
Once you have selected the most appropriate certification scheme, you will be ready to prepare for the assessment and demonstrate your commitment to cybersecurity best practices.
Step 3: Implement recommended security controls
Implementing recommended security controls is a critical step in fortifying your organisation’s cyber defences and ensuring comprehensive protection against potential digital threats. This stage transforms your certification preparation from theoretical planning into practical, actionable security measures.
Wikipedia outlines five essential technical controls that form the foundation of robust cybersecurity protection. These controls are designed to shield your organisation from internet based threats and provide a fundamental level of digital defence applicable to businesses of all sizes.
The five key security controls you will need to implement include:
Boundary firewalls and internet gateways
Secure configuration of systems and devices
User access control and authentication mechanisms
Comprehensive malware protection
Systematic patch management and software updates
Each control requires specific attention and strategic implementation. Boundary firewalls should be configured to restrict unauthorised network access, while secure configuration involves hardening your systems by removing unnecessary software and disabling default accounts. Access control demands robust user authentication processes, including strong password policies and multi factor authentication where possible.
Pro tip: Do not approach these controls as a one time implementation. Treat them as living security protocols that require continuous monitoring, regular review, and adaptive management to remain effective against evolving cyber threats.
Once you have systematically implemented these security controls, you will have established a robust foundation for your cybersecurity infrastructure and significantly improved your readiness for certification assessment.
Step 4: Complete certification application and validation
Completing your cyber security certification application is the pivotal moment where your preparation transforms into official recognition of your organisation’s digital defence capabilities. This crucial stage involves meticulously documenting your security controls and submitting them for comprehensive professional assessment.
The National Cyber Security Centre provides detailed guidance on the certification process, which typically involves two primary pathways. The first is a verified self assessment questionnaire for Cyber Essentials certification, while the second level requires independent technical verification for Cyber Essentials Plus.
When preparing your application, you will need to gather and prepare:
Comprehensive documentation of your implemented security controls
Network and system configuration details
Evidence of secure access management practices
Documented patch management procedures
Malware protection and firewall configuration records
The validation process requires absolute transparency and accuracy. Assessors will carefully review your submitted documentation, looking for consistent evidence that demonstrates your organisation meets the required security standards. Be prepared to provide clear, detailed explanations of your security mechanisms and be ready to answer follow up queries.
Pro tip: Treat your certification application as more than a bureaucratic exercise. View it as an opportunity to demonstrate your commitment to robust cybersecurity and showcase your organisation’s professional approach to digital protection.
Once your application is submitted and validated, you will have achieved a significant milestone in your cybersecurity journey, proving your organisation’s dedication to maintaining a secure digital environment.
Step 5: Maintain compliance with continuous monitoring
Continuous monitoring is the cornerstone of maintaining your hard earned cybersecurity certification and ensuring your organisation remains resilient against evolving digital threats. This final stage transforms your certification from a static achievement into a dynamic, adaptive security strategy that protects your business throughout the year.
The Government Cyber Security Policy Handbook emphasises the critical importance of building ongoing monitoring capabilities that meet robust security standards. Continuous monitoring goes beyond periodic assessments, creating a proactive approach that identifies and addresses potential vulnerabilities in real time.
To effectively maintain compliance, you will need to implement several key practices:
Regular vulnerability scanning and assessment
Automated security monitoring systems
Periodic review of access controls and user permissions
Systematic software and system patch management
Comprehensive incident response and reporting mechanisms
Your monitoring strategy should include automated tools that provide real time insights into your network security, coupled with manual reviews that capture nuanced risks that automated systems might miss. This approach ensures a comprehensive view of your organisation’s security posture, enabling swift identification and mitigation of potential threats.
Pro tip: Do not treat compliance as a static destination. View it as an ongoing journey of continuous improvement, where each review and update strengthens your organisation’s digital defences.
By maintaining a rigorous and proactive approach to continuous monitoring, you will not only sustain your certification but also build a robust, adaptive cybersecurity infrastructure that evolves with your business.
Simplify Your Journey to Cyber Essentials Certification with Freshcyber
Achieving and maintaining Cyber Essentials certification can feel overwhelming. This guide highlights common challenges UK SMEs face, from understanding compliance requirements to implementing effective security controls and managing continuous monitoring. If you want to move beyond complexity and uncertainty Freshcyber offers clear, practical support tailored for busy business owners and lean IT teams.
Our expert team specialises in accelerating certification through end-to-end guidance aligned with Cyber Essentials standards, helping you protect your organisation while building client trust. With continuous vulnerability management as a core service, Freshcyber ensures your security stays strong year-round without last-minute pressure. Discover how our Cyber Essentials and Compliance solutions directly address the key goals outlined in the article.

Take control of your cybersecurity certification today and avoid costly delays or gaps in protection. Visit Freshcyber now to learn how our services keep Cyber Essentials certification simple and stress-free with continuous security oversight. Start your journey to proven compliance and peace of mind right away.
Frequently Asked Questions
What are the first steps to assess my current cybersecurity needs?
To assess your current cybersecurity needs, start by reviewing your existing IT infrastructure and security practices. Map out current security tools, employee access levels, and incident response capabilities to identify vulnerabilities, and do this at least annually to stay updated.
How do I choose the right cybersecurity certification for my SME?
To choose the right cybersecurity certification, evaluate the complexity of your IT infrastructure and any specific regulatory requirements for your sector. Consider starting with Cyber Essentials, as it provides a solid foundation and can usually be achieved within a few weeks.
What security controls should I implement for certification?
You should implement five key security controls: boundary firewalls, secure system configurations, user access control, malware protection, and patch management. Focus on ensuring robust user authentication processes, which should be established and updated regularly to maintain security.
How do I prepare for the certification application process?
Prepare for your certification application by compiling comprehensive documentation of your security controls, including network and system configurations. Create this documentation before you begin the application to ensure accuracy and clarity throughout the process.
What practices can I adopt for continuous monitoring after certification?
For continuous monitoring, implement regular vulnerability scans, automated security monitoring systems, and periodic reviews of access controls. Establish a proactive strategy to identify and address vulnerabilities, aiming to conduct reviews at least quarterly to enhance your overall security posture.
How can I maintain compliance after receiving my certification?
To maintain compliance, adopt a routine of continuous monitoring that includes both automated tools and manual reviews. Develop a timeline to review your security measures, ideally every month, to adapt and strengthen your cybersecurity infrastructure as threats evolve.
Recommended
Comments